Secure Office-Based Outsourcing in the Philippines
Your team works from a fully controlled office in Cebu IT Park, Philippines.

How We Keep Your Data Secure And Private
Device & System Security
All work is carried out on company-managed devices within a controlled setup.
- Company-issued computers configured under central security policies
- Device encryption and system monitoring
- Secure cloud storage enforced
- USB storage disabled
- Restricted software installation
- Secure login and password controls
This means your data stays within controlled systems at all times.

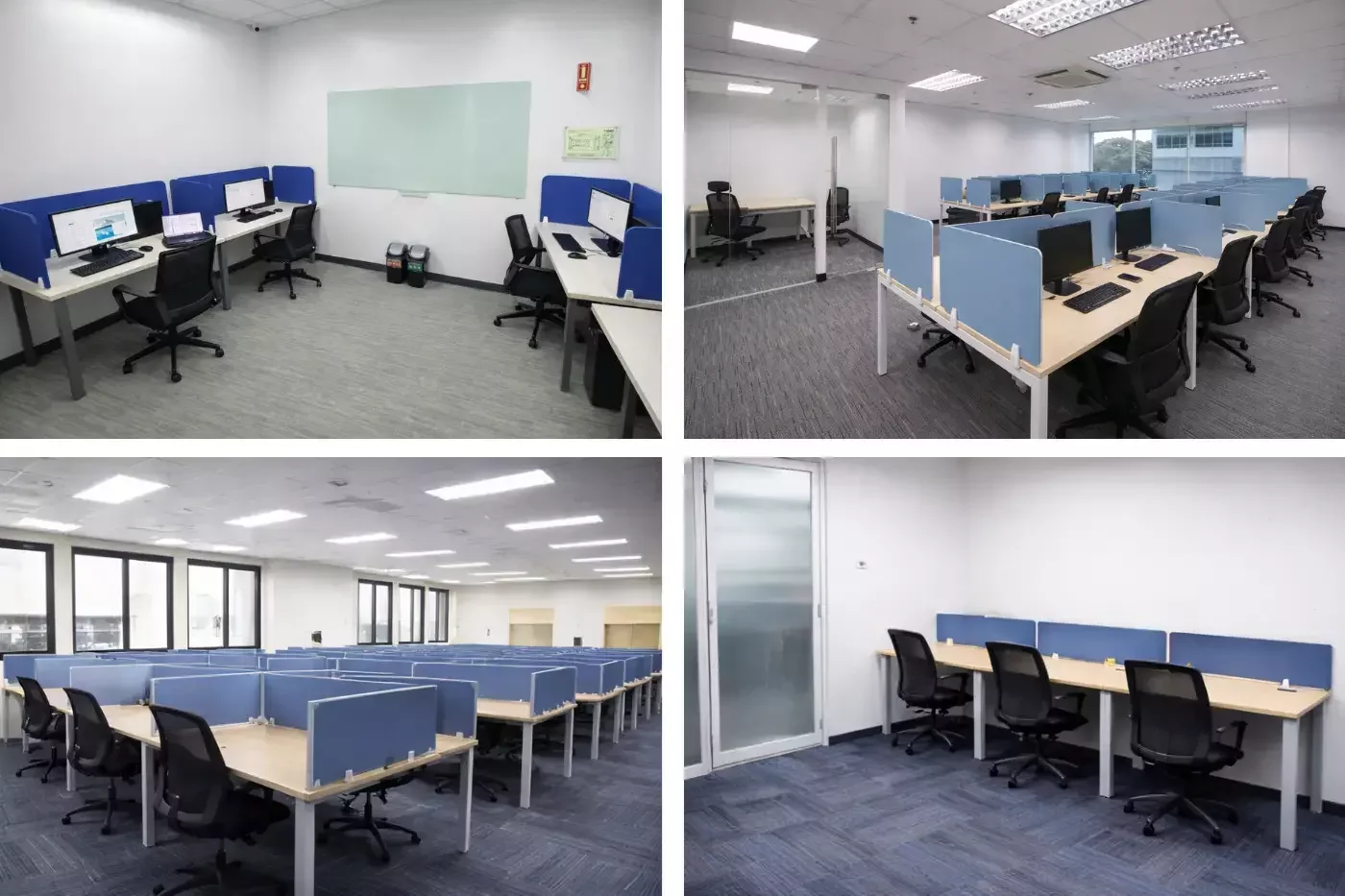
Secure Office Environment
Your team works from a professional office in Cebu IT Park.
- Biometric access control
- CCTV monitoring across working areas
- 24/7 building security
- Restricted physical access to authorised staff only
This means your team operates in a secure, managed environment, not from home setups.
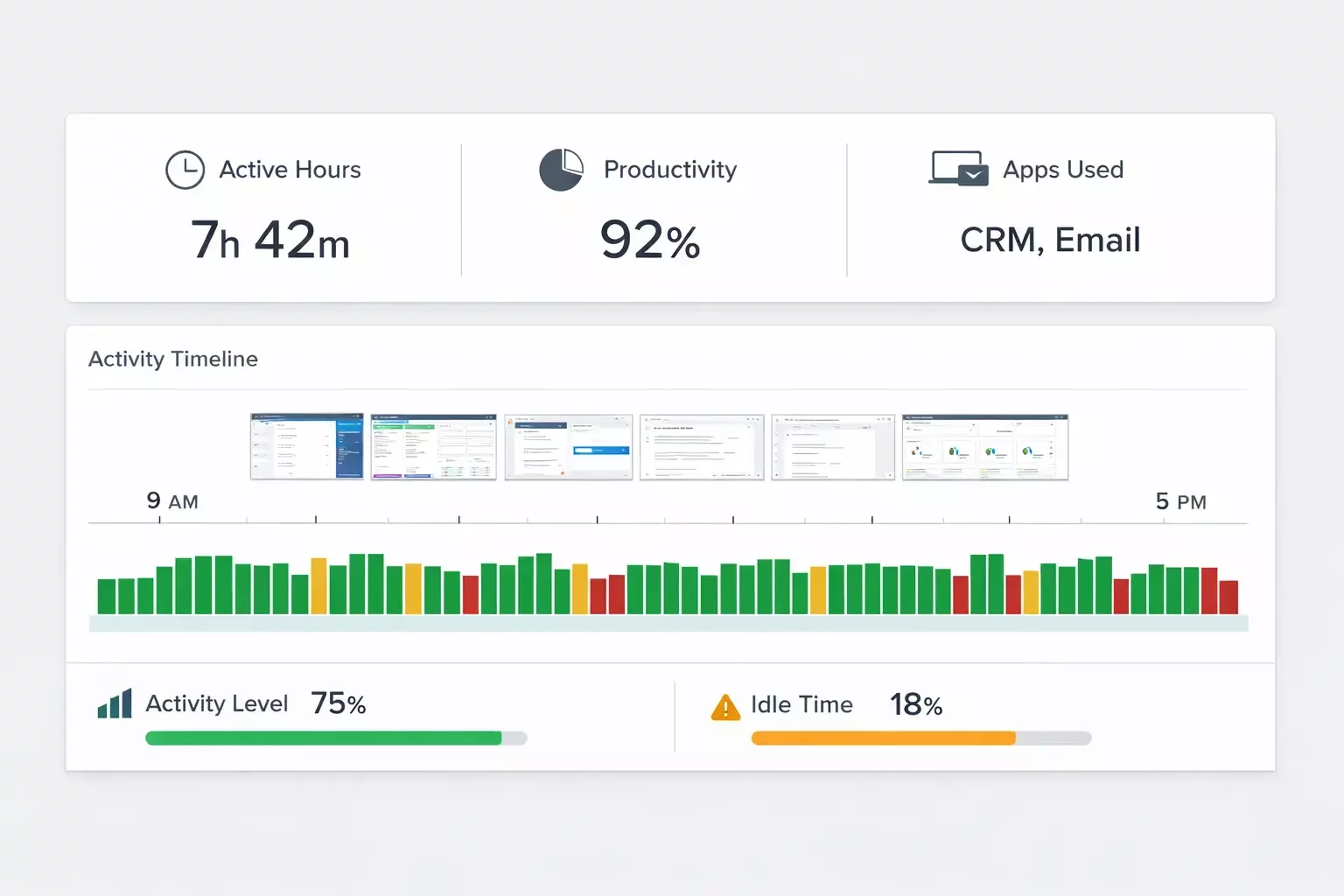
Visibility & Tracking
You have clear visibility over your team.
URL and website tracking
Activity and work tracking
Break and time tracking
Structured working hours
On-site supervision
You can see when your team is working and how work is being done.
Our Operating Model
Confidentiality & Legal Protection
All staff sign strict confidentiality agreements as part of their employment.
Employment contracts include data protection and non-disclosure clauses. Client NDAs can also be executed where required.
Access to systems and client information is role-based and permission controlled.
This means that sensitive information is only accessible to authorised personnel under enforceable legal agreements.
Compliance & Data Handling Standards
We operate documented internal policies covering data access, password standards, system usage, and device management.
User access is centrally managed and regularly reviewed. Staff onboarding and offboarding is controlled to ensure permissions are granted and revoked appropriately.
This means that data handling is structured, monitored, and not left to individual discretion.
Business Continuity & Operational Stability
Our office infrastructure includes enterprise-grade internet with backup lines and contingency planning procedures.
Company devices are standardised and replaceable, ensuring minimal disruption if hardware issues occur.
Operational oversight ensures continuity across teams.
This means that your offshore function remains stable, responsive, and resilient in unexpected situations.
Frequently Asked Questions
How we secure your operations and reduce risk.

